Share Blog Post
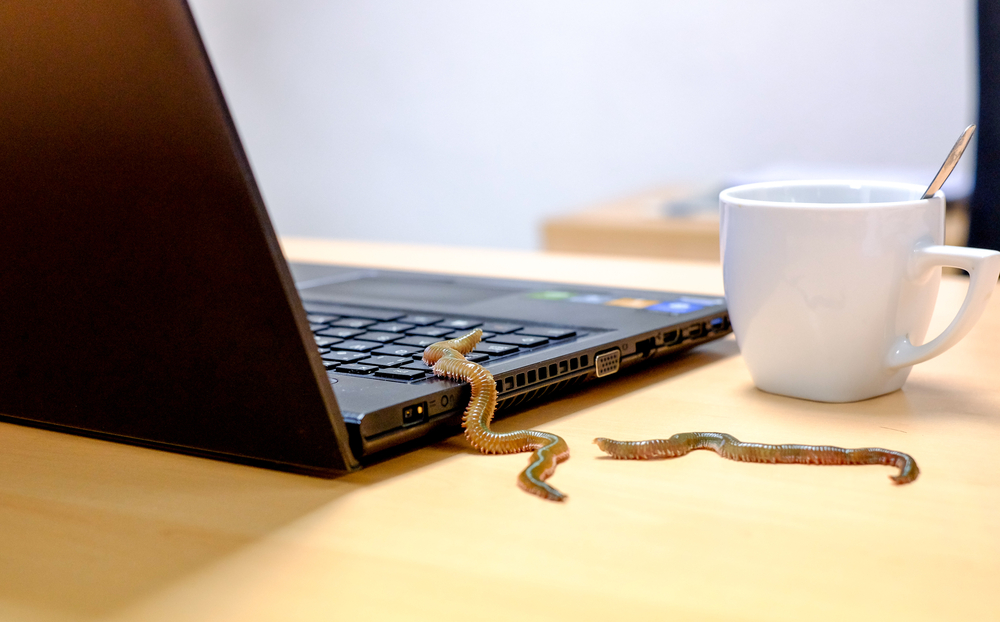
Top Malware Reported in the Last 24 Hours
DoubleDoor IoT botnetSecurity researchers have found an IoT botnet, dubbed DoubleDoor, that bypasses firewall protections and modem security using two backdoor exploits. DoubleDoor botnet uses a randomized string in every attack, making it difficult to detect.
Olympic Destroyer
The malware almost wreaked a havoc in the 2018 Winter Olympic games, causing damage to internal Wi-Fi network and television systems. Using a data-wiping mechanism, Olympic Destroyer deleted files on network shares. The malware has a self-patching mechanism for mutating and evolving from each infected host to another.
Top Vulnerabilities Reported in the Last 24 Hours
Meltdown and Spectre assessment toolMicrosoft released an assessment tool for Windows to check if your PCs are vulnerable to Meltdown and Sprectre flaws. You can access these capabilities through the free Windows Analytics service. The features are available on Pro, Enterprise, and Education editions of Windows 7 with Service Pack 1, Windows 8.1, and Windows 10.
Security bypass flaw
It has been found that Microsoft Edge is vulnerable to a security-bypass vulnerability, CVE-2018-0771. By exploiting this vulnerability, hackers can bypass some of the security restrictions and force the browser to disclose sensitive information.
Adobe releases security update
Security updates have been released for Adobe Acrobat and Reader for Windows and Macintosh. These updates are aimed at patching critical vulnerabilities that could allow an attacker to take control of the affected system. Around 39 bugs have been patched.
Top Breaches Reported in the Last 24 Hours
BitGrail cryptocurrency exchange hackedBitGrail cryptocurrency exchange platform has been hacked recently, with hackers stealing 17 million Nano--a cryptocurrency formerly known as RaiBlocks--that is worth around $195 million. The breach took place due to poor defense tactics.
Misconfigured Cloud databases
A data repository of customer information--including personally identifiable information and bank account details--has been left exposed by the Maryland Joint Insurance Association (MDJIA). The database also exposed MDJIA access credentials for ISO ClaimSearch, a third-party insurance database.
A brand marketing firm, Octoly left open internet access to an AWS S3 bucket, resulting in data leakage of sensitive personal details of more than 12,000 social media influencers used in its marketing campaigns.
Tags
Posted on: February 14, 2018
More from Cyware
Stay updated on the security threat landscape and technology innovations at Cyware with our threat intelligence briefings and blogs.