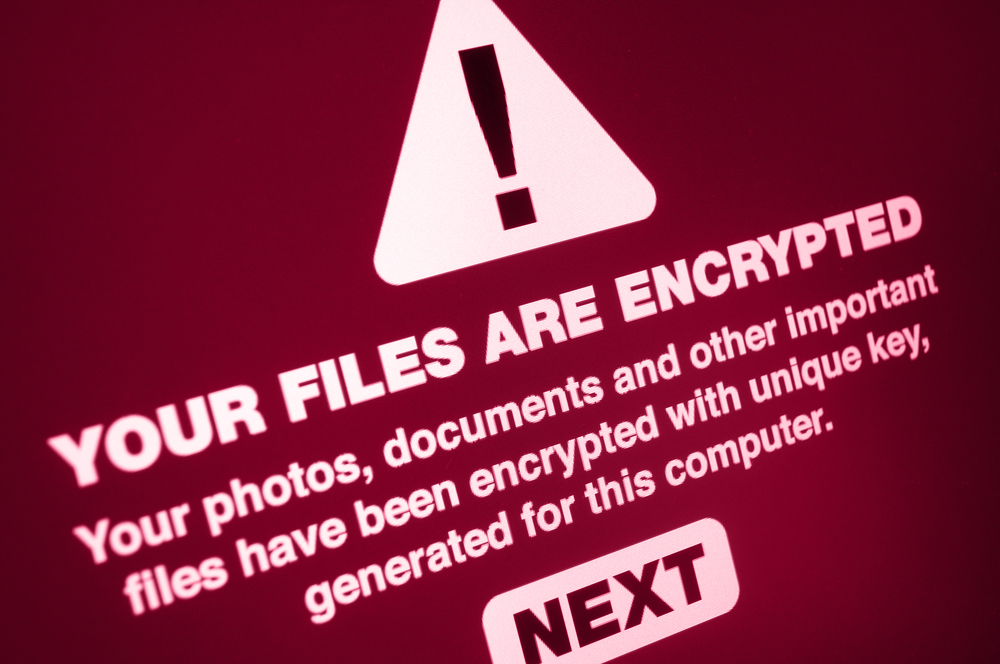
The scare that ransomware caused with two major attacks -- WannaCry and NotPetya. These attacks caused hundreds of dollars in damages while hackers continued to laugh their way to the banks and continued to target systems across the globe. Although, after the incidents, there were several learnings for all organizations -- small, medium, and large -- to take proactive actions to prevent big damage. The most consistent defense against ransomware continues to be good backups and a well-tested restore process. Companies that consistently back up their data and can quickly detect a ransomware attack should be able to restore their data and operations with a minimum of disruption.
What’s even more striking is that some ransomware like NotPetya pretending to be a regular malware but later turning out to be wipers. In such cases, users won’t get back their data even when the ransom is paid — making the ability to restore from a backup even more critical.
In the wake of colossal incidents around the world, cybersecurity industry has witnessed a spike in ransomware protection solutions. Nevertheless, the strategy is straightforward: Encrypt the backup and individuals or companies are likely to lose the ability to restore data and are more likely to pay a ransom. Attackers are escalating their efforts beyond infecting single workstations and aim to destroy the backups, too.
The cybersecurity community brings you three recommendations to help enterprises secure your backups against ransomware onslaughts.
1. Keep a watch when using file-sharing services
When working in a networked environment, a centralized data repository makes it easy to backup data from all the computers. But, this data architecture has serious vulnerabilities. Most ransomware programs encrypt infected system drives and any connected drives as well. Making your backups unusable. Thus, any company with a network file server needs to backup the data to a separate system.
2. Keep your backup process transparent
The sooner you detect a ransomware infection, the earlier you mitigate the damage and prevent significant corruption of data. You should always be on the lookout to watch any early signs of a ransomware infection from the backup process. Incremental backups will ruin the entire backup as every file is essentially changed and the encrypted files can’t be compressed or deduplicated. Thus, you should monitor your vital metrics such as capacity utilization from the backup process on regular basis.
3. Contemplate your solutions
If ransomware can directly access backup images, then it will be very challenging if not impossible to stop it from encrypting corporate backups. For that reason, a purpose-built backup system that abstracts the backup data will be able to prevent ransomware from encrypting historical data.
By separating backups from your normal operating environment and making sure the process is not running on a general-purpose server and operating system, your backups can be hardened against attack. Backup systems based on the most commonly targeted operating system, Microsoft Windows, are prone to be attacked and make it much harder to protect your backup data.

Publisher








/https://cystory-images.s3.amazonaws.com/shutterstock_341144111.jpg)
/https://cystory-images.s3.amazonaws.com/shutterstock_110361224.jpg)
