Alone, You May Be Secure, But Together You’re Resilient
Cyware Collaborate enhances situational awareness by unifying advisory management, collaboration, and secure threat sharing, enabling security teams and communities to act on trusted intelligence, respond faster, and build resilience together.
30K+
Global Organizations Leverage the Cyware Platform
85%
Of Major ISACs Use the Cyware Platform
How Cyware Collaborate Amplifies Situational Awareness
Break silos and respond faster with automated advisories, collaborative workflows, and real-time bi-directional intelligence sharing for stronger collective defense.
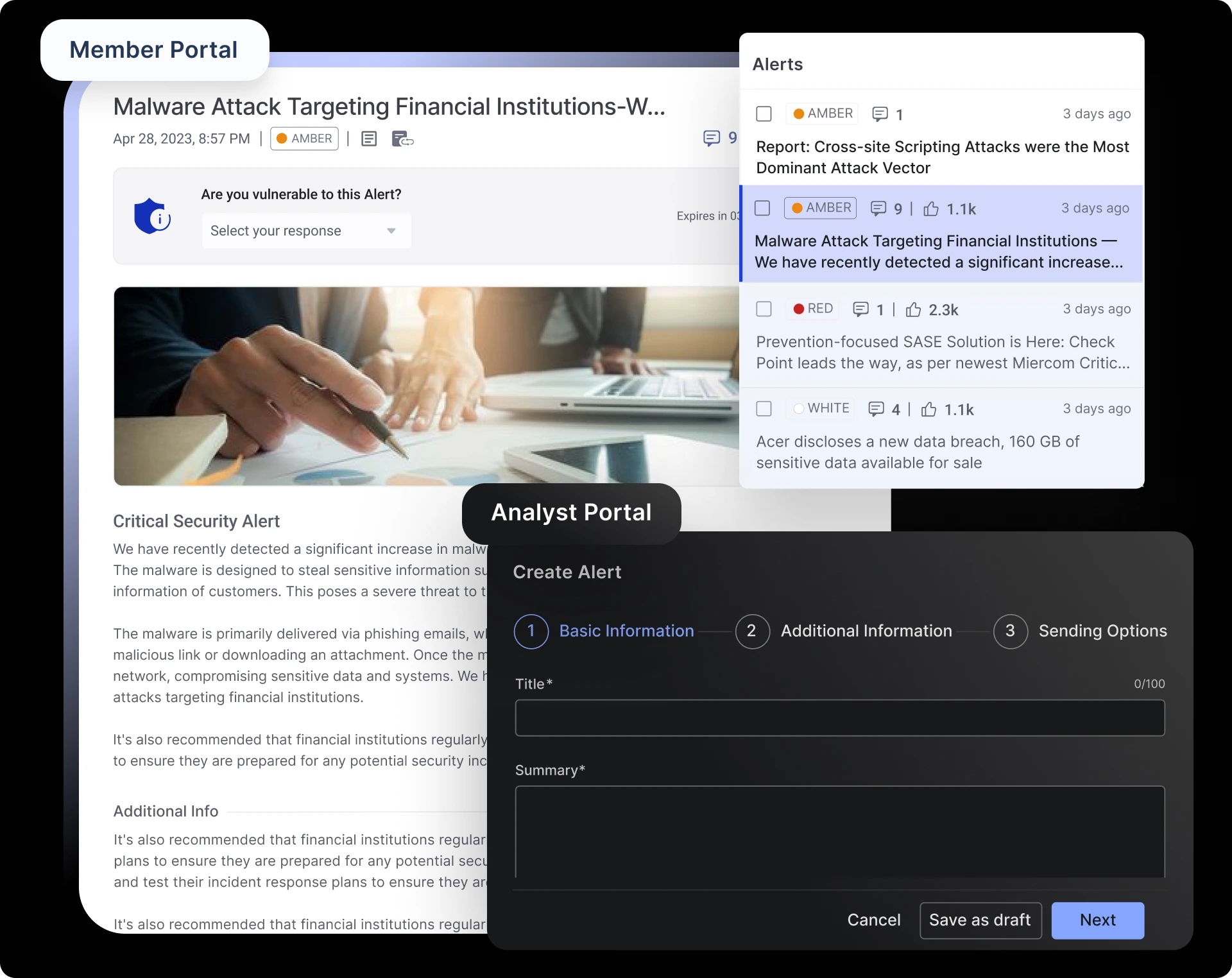
Centralized Threat Advisory Management
Centralized Threat Advisory Library with Curated Cyware Security Advisories
Access, store, and act on advisories, reports, policies, and research, including access to curated Cyware Security Advisories for enhanced situational awareness.
Secure Analyst Portal for Creating and Sharing Intelligence
A dedicated workspace to create, manage, and disseminate intelligence with precision, including customized advisories tailored to your members.
Customized Member Portal for Timely Access to Strategic Threat Intelligence
Enable security teams and organizations to access advisories and intelligence in real-time for faster decision-making.
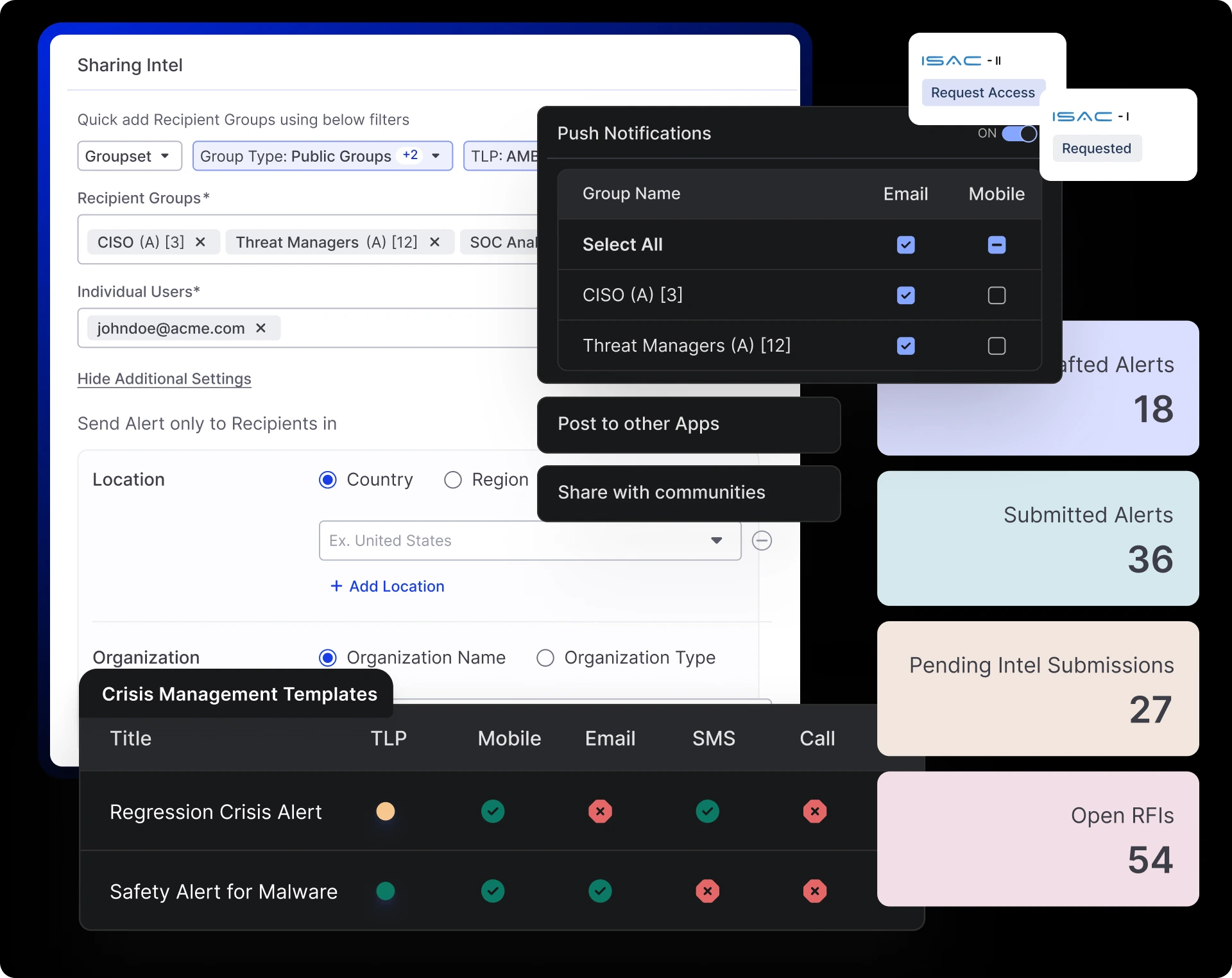
Comprehensive Situational Awareness & Threat Sharing
Custom Dashboards and Reporting
Track intel flow, member activity, incident stats, surveys, and engagement to refine priorities.
Multi-Channel Threat Context Sharing
Deliver role, location, and business-aligned intel across web, mobile, and portals with granular access controls.
Secure ISAC-to-ISAC Sharing and Crisis Management
Securely exchange intelligence between ISACs and leverage ready-to-use crisis templates for coordinated response.
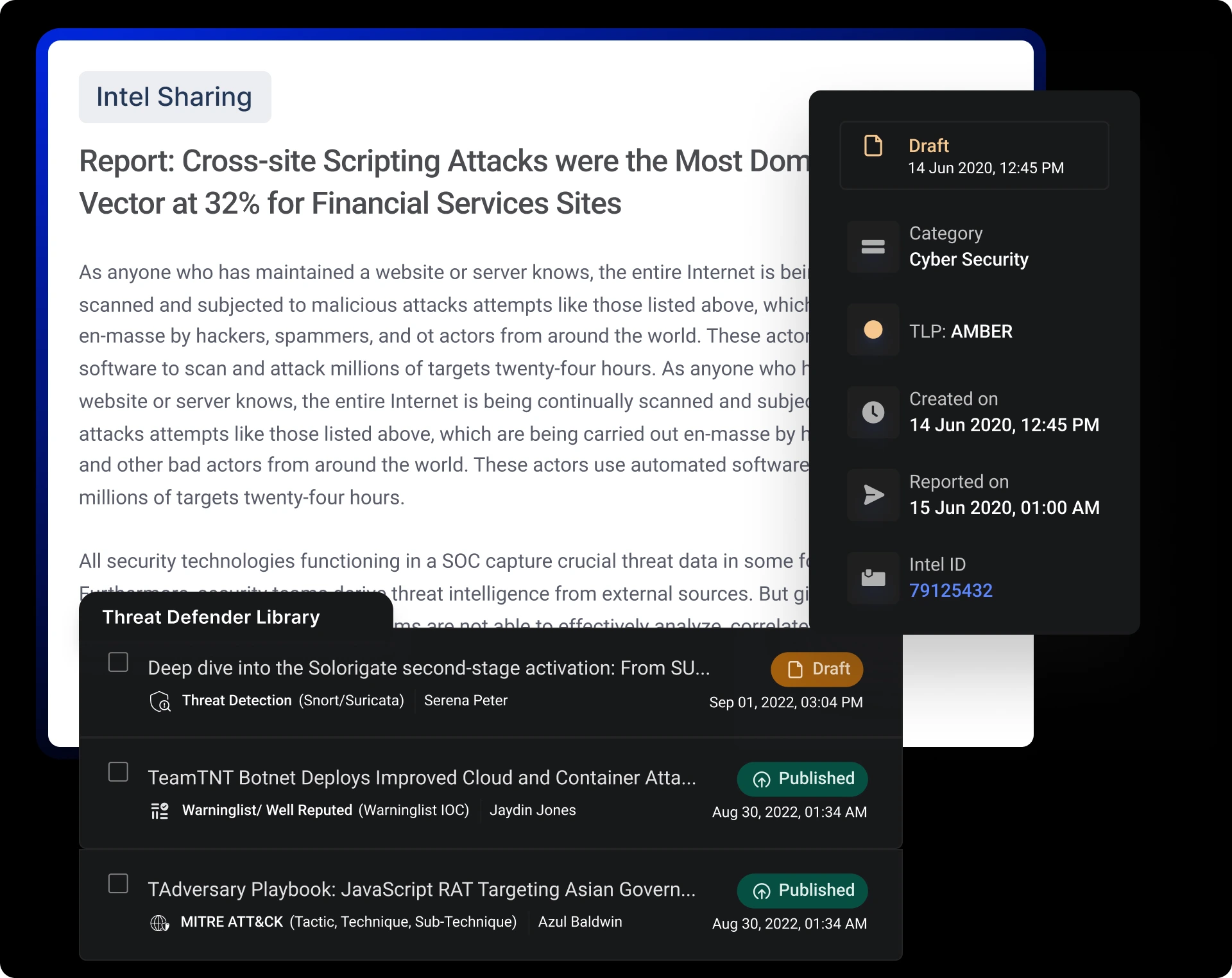
Defender Collaboration for Collective Defense
Threat Defender Library
Analyze the full threat intel context to automatically generate production-ready Threat Defender Library rules and validated SIEM queries, ensuring faster detection coverage with minimal manual toil.
Investigative Collaboration and Compromised Credential Management
Analyze threats, design effective mitigation strategies, and manage compromised credentials by monitoring, validating, and securely sharing and acting on intelligence across trusted communities.
Trusted External Collaboration
Securely share intel with ISACs, ISAOs, and CERTs to enable timely, large-scale collective defense.
Cross-Functional Workflows for Coordinated Action
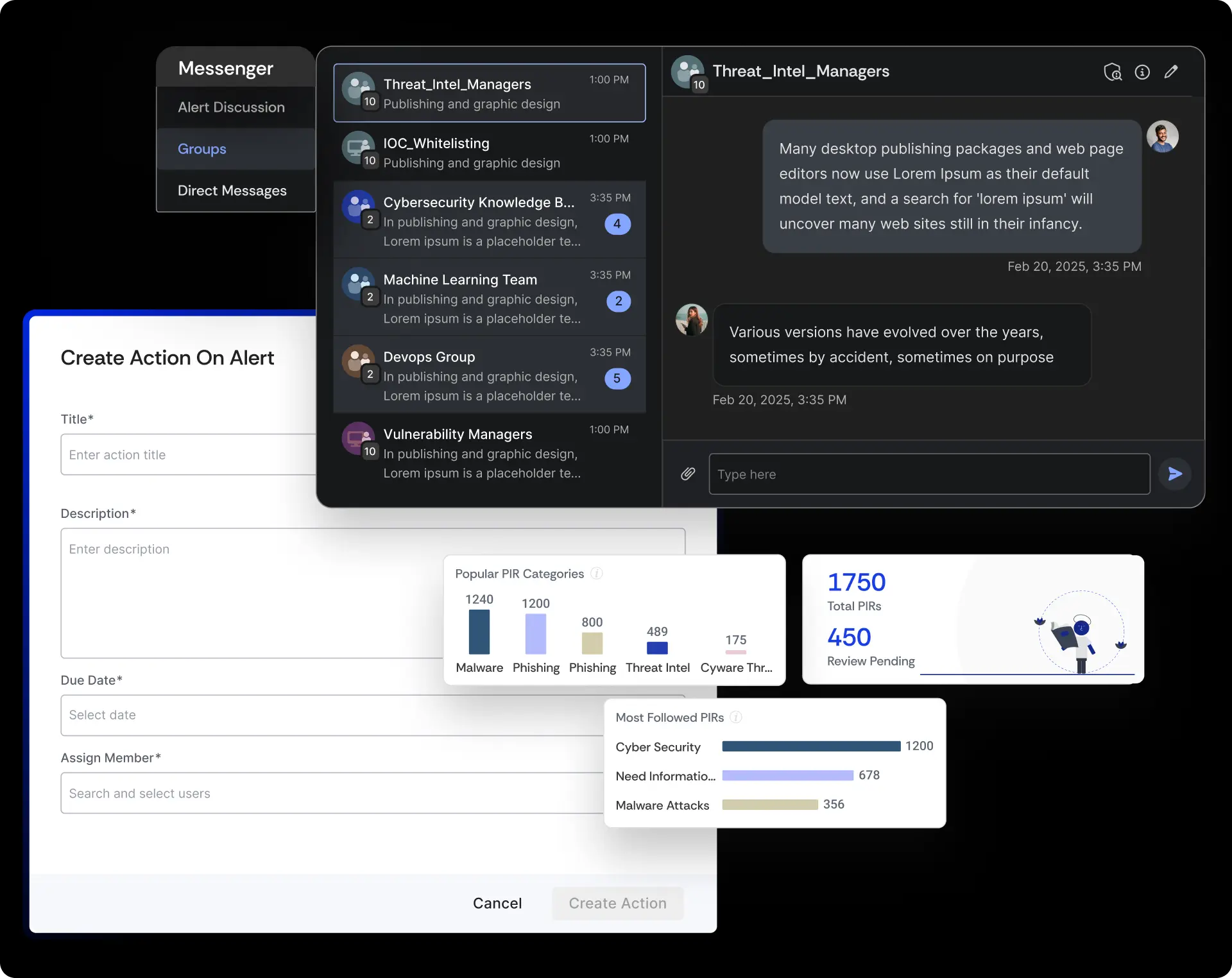
Secure Communication and Group Discussions
Use built-in messaging and topic-based groups to drive collaboration and enable bi-directional threat intelligence sharing for real-time threat action.
Integrated Incident Reporting and Tracking
Report incidents, track investigations, and maintain accountability.
Prioritized Intelligence Requests
Submit structured requests to receive timely, relevant intel for strategic decision-making.
Automated Collective Defense for Seamless, Real-Time Threat Response
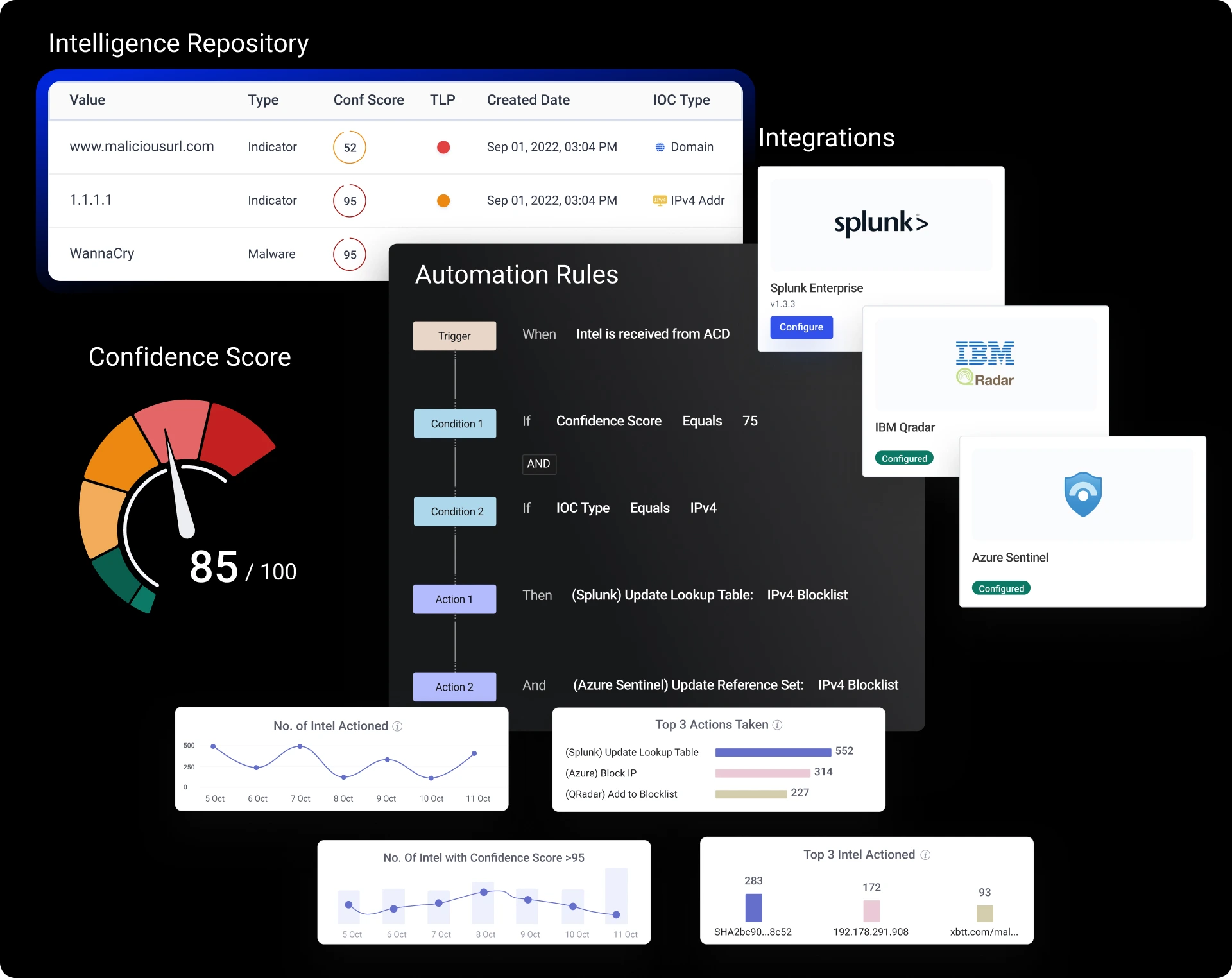
Automated Bi-Directional Threat Intelligence Sharing
Collaborate with ISACs, ISAOs, and trusted communities through bi-directional threat intel sharing to exchange and act on indicators in real-time.
Seamless Integrations & Automation
Connect with Splunk, Microsoft Sentinel, QRadar, and more to detect, share, and respond instantly.
Centralized Intelligence Repository
Maintain a single source of truth for threat data to simplify management and collective analysis.
Cyware Collaborate is a secure, bi-directional threat intelligence sharing and collaboration platform. It enables organizations to aggregate intelligence from multiple sources, contextualize it, and share it in real time with internal teams and trusted external partners. It also provides structured collaboration tools to coordinate responses and collectively improve defense.
Explore All Our Offerings
Learn how Cyware is your go-to platform to unify, operationalize, respond to, and securely share threat intelligence.