The Threat Intelligence Enrichment Challenge
Without the Right Context, Threats Get Misprioritized and Response Is Delayed
Threat feeds flood analysts with thousands of indicators daily without enrichment teams wasting hours chasing false positives and miss real threats hidden in the noise.
With Cyware, Enrich and Contextualize Threat Intelligence Automatically
Automatically enrich threat intelligence, add context, prioritize smarter, and streamline workflows for faster, more accurate responses.
Context-Rich Intel at Scale
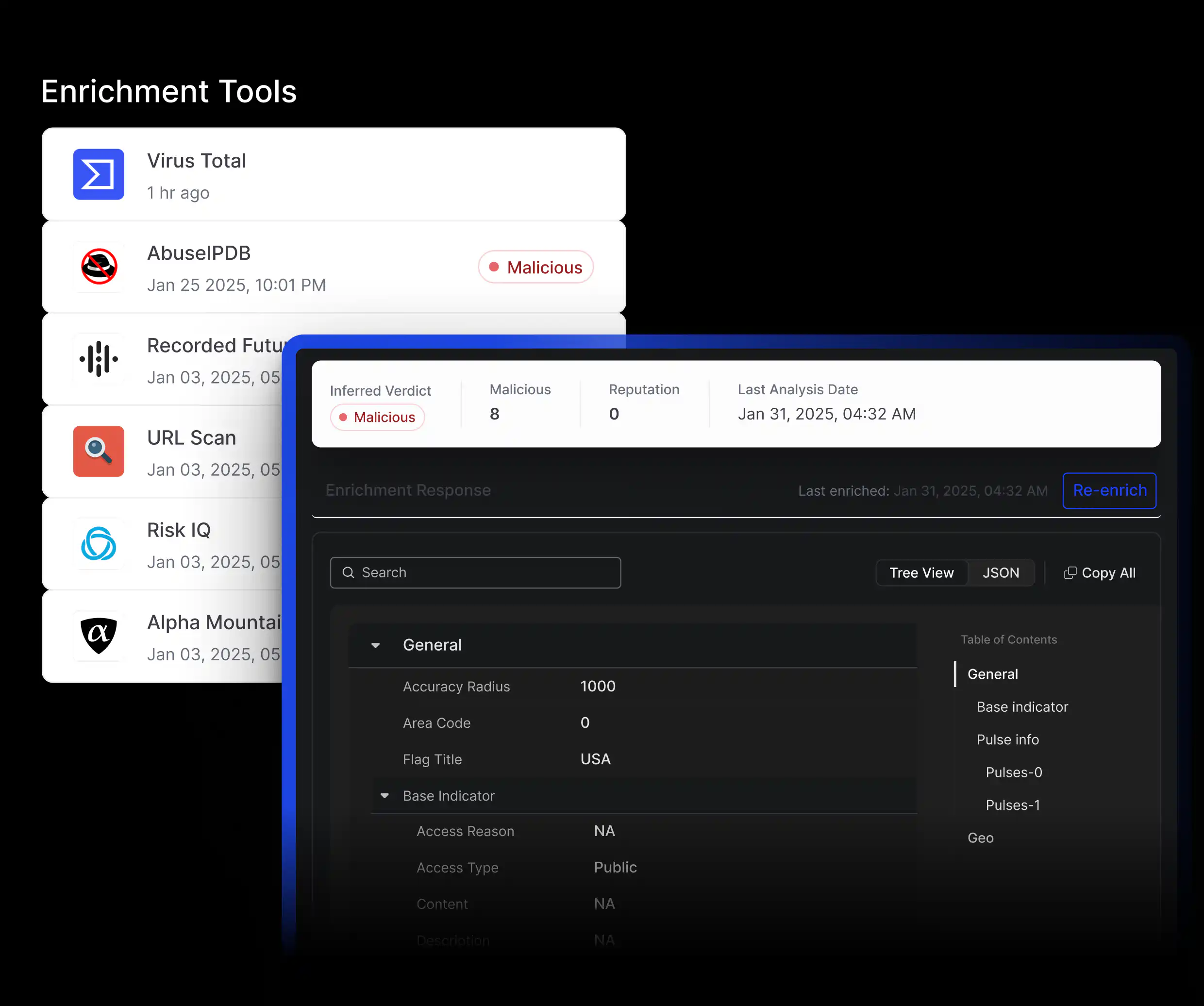
Use pre-built connectors to tools like VirusTotal, Shodan, and AbuseIPDB to automatically enrich IOCs with context such as source reliability, geography, malware links, and threat actor associations.
Smarter Triage and Prioritization
Correlate threat indicators with internal telemetry, map them to MITRE ATT&CK techniques, apply custom risk scores, and instantly surface high-priority threats for faster investigations.
Enrichment Tool Management
Control costs and optimize usage with quotas for enrichment tools while ensuring critical processes run smoothly. Configure enrichment policies to auto-enrich threat data objects like IPs, hashes, domains, vulnerabilities, and URLs.
Automated Rules and Playbooks
Trigger enrichment through rule-driven or playbook-based conditions to automate recurring processes, streamline workflows, and free analysts from repetitive manual effort.
Context-Rich Intel at Scale
Use pre-built connectors to tools like VirusTotal, Shodan, and AbuseIPDB to automatically enrich IOCs with context such as source reliability, geography, malware links, and threat actor associations.
Smarter Triage and Prioritization
Correlate threat indicators with internal telemetry, map them to MITRE ATT&CK techniques, apply custom risk scores, and instantly surface high-priority threats for faster investigations.
Enrichment Tool Management
Control costs and optimize usage with quotas for enrichment tools while ensuring critical processes run smoothly. Configure enrichment policies to auto-enrich threat data objects like IPs, hashes, domains, vulnerabilities, and URLs.
Automated Rules and Playbooks
Trigger enrichment through rule-driven or playbook-based conditions to automate recurring processes, streamline workflows, and free analysts from repetitive manual effort.
Threat intelligence enrichment is the process of enhancing raw threat data with additional context and information to make it more actionable for security teams. This process involves aggregating, correlating, and analyzing data from various sources to provide a comprehensive view of potential threats. It helps transform vague alerts into detailed intelligence, enabling security teams to prioritize and respond to threats more effectively.