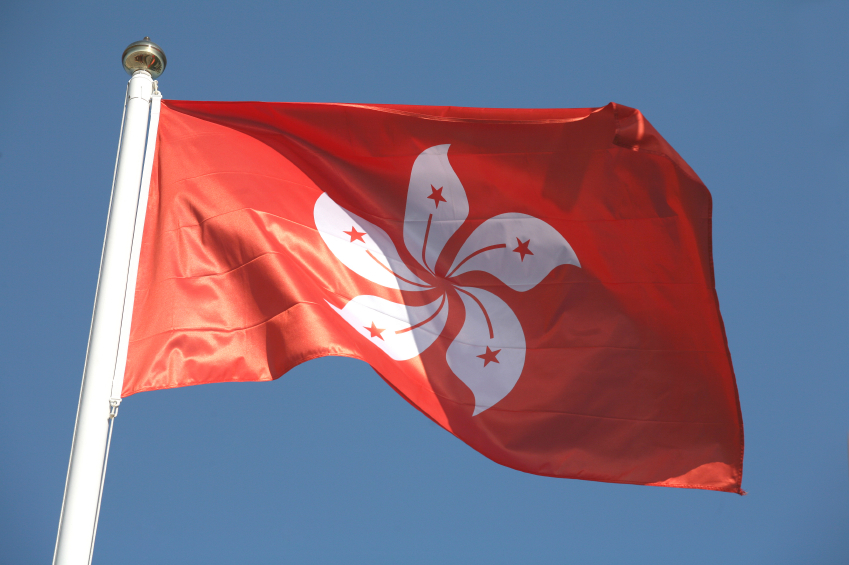
A new cyberespionage malware, dubbed DazzleSpy, has been discovered infecting macOS by abusing a Safari exploit via a watering hole attack. The attack is reportedly aimed at politically active and pro-democracy people in Hong Kong.
About the attack campaign
ESET has linked the ongoing campaign to an unknown threat actor with strong technical capabilities.
- First, the attackers targeted a genuine website of pro-democracy internet radio station D100 Radio in Hong Kong, injecting malicious iframes between September 30 and November 4, 2021.
- Subsequently, a fraudulent website fightforhk[.]com was registered for luring liberation activists.
- In the next step, tampered code was used to load a Mach-O file by abusing a remote code execution flaw (CVE-2021-1789) in WebKit. This flaw has already been mitigated by Apple in February 2021.
- Further, the malware triggers the execution of the intermediate Mach-O binary that exploits the CVE-2021-30869 flaw in the kernel component to execute the next stage malware as a root user.
This campaign has similarities with LightSpy iOS malware described by Trend Micro and Kaspersky. It is distributed in the same way, using iframe injection on websites and WebKit exploits for Hong Kong people.
Dissecting DazzleSpy
DazzleSpy comes with multiple sets of functionalities to control and exfiltrate files from an infected computer system. In addition, the threat has a number of other features as well, such as:
- Harvesting system information, executing arbitrary shell commands, and dumping iCloud Keychain by using the CVE-2019-8526 exploit if a targeted macOS version is lower than 10.14.4.
- Starting or terminating a remote screen session and deleting itself from the infected systems.
Conclusion
The use of multiple exploits shows the strong technical capabilities of the threat group behind this campaign. Moreover, the use of watering-hole attacks indicates that the attackers engage in highly targeted attacks. Deploying the right anti-malware solutions and ensuring a proper patch management program can be of big help. Also, cybersecurity teams must track the IOCs provided by researchers for better protection against such threats.

Publisher








/https://cyware-ent.s3.amazonaws.com/image_bank/shutterstock_465668897.jpg)
/https://cyware-ent.s3.amazonaws.com/image_bank/79f7_shutterstock_1918119194.jpg)
