Newly discovered RobinHood ransomware variant drops four ransom notes at once after encryption
- RobinHood renames the encrypted files something similar to Encrypted_b0a6c73e3e434b63.enc_robinhood.
- The ransomware drops 4 ransom note with different names at the same time.
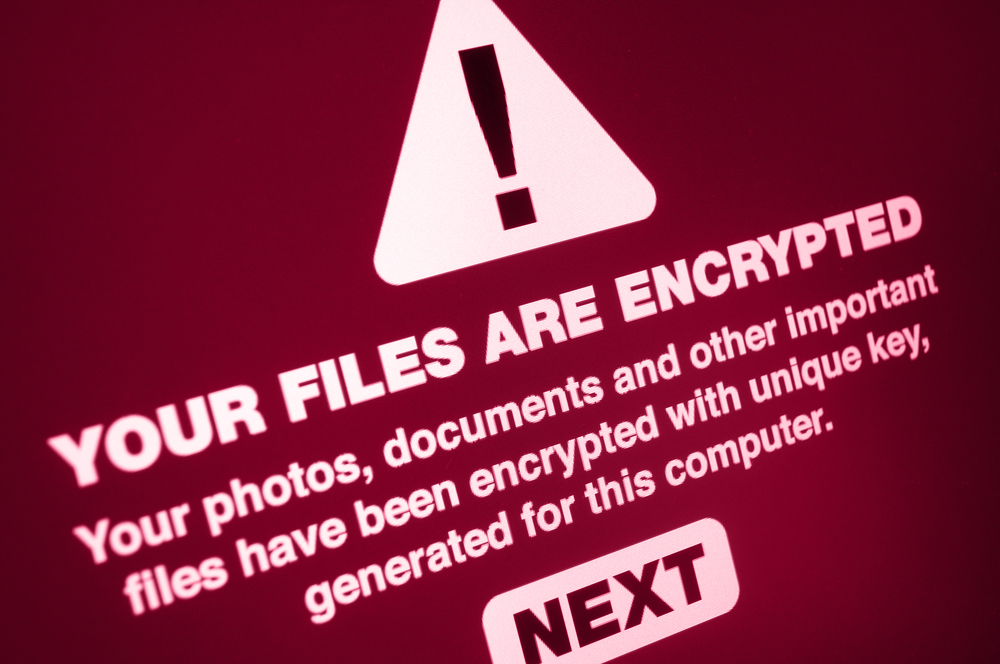
A new ransomware named RobinHood has been found targeting computers within an entire network. The operators of the ransomware are so particular about victims’ privacy that they delete the encryption keys and IP addresses after the payment is received.
How does the ransomware operate - The propagation method of the ransomware is unknown. However, once it is installed, RobinHood renames the encrypted files something similar to Encrypted_b0a6c73e3e434b63.enc_robinhood.
After this, the ransomware drops 4 ransom note with different names at the same time. The names of these notes are _Decryption_ReadMe.html, _Decrypt_Files.html, _Help_Help_Help.html, and _Help_Important.html.
What do these ransom notes say - The ransom notes include information regarding what happened to the victim’s files, the ransom amount and links to the TOR sites.
The TOR links are the ones where the victim is required to leave a message for the attackers or where they can decrypt 3 files of up to 10MB in size for free.
The ransom varies depending on the number of computers that are encrypted.
“For example, in a ransom note seen by BleepingComputer, the ransom was 3 bitcoins per computer or 7 bitcoins for the network,” Bleeping Computer noted.
By the fourth day, the ransom increases by $10,000 per day if the victim fails to pay on time.
Once the ransom is received, the attackers delete the encryption key and IP address to protect the privacy of the victim.

Publisher








/https://cystory-images.s3.amazonaws.com/ultrasound-scan.jpg)
/https://cystory-images.s3.amazonaws.com/shutterstock_500903536.jpg)
