- Attackers infected the systems of Altran Technologies with LockerGoga ransomware that spread throughout the company’s network affecting operations in some European countries.
- Atran Technologies shut down its IT network and all applications to protect its client data.
Altran Technologies is a global innovation and engineering consulting company located in France. The French company announced on 28 January 2019 that it suffered a cyber attack on January 24, 2019, which affected operations in some European countries. The company shut down its IT network and all applications to protect its client data.
“To protect our clients, employees, and partners, we immediately shut down our IT network and all applications. The security of our clients and of data is and will always be our top priority. We have mobilized leading global third-party technical experts and forensics, and the investigation we have conducted with them has not identified any stolen data nor instances of propagation of the incident to our clients,” Atran Technologies said in a press release.
LockerGoga Ransomware
Security researchers with sufficient evidence confirmed that the systems of Altran Technologies were infected with the LockerGoga ransomware that spread throughout the company’s network.
The cyber attack against Altran Technologies was first disclosed by an individual named ‘Laurent’ on Twitter on January 25, 2019. To which, a security researcher replied with a malware sample that was uploaded to VirusTotal, stating that the malware was behind the attack against Altran Technologies.
The malware sample was uploaded to VirusTotal for the first time on January 24, 2019, from Romania, and later the same day from the Netherlands. The sample was detected as ‘LockerGoga’. The name of the ransomware is based on the path used for compiling the source code into an executable. The path was discovered by MalwareHunterTeam. X:\work\Projects\LockerGoga\cl-src-last\cryptopp\src\rijndael_simd[.]cpp
More details on the ransomware
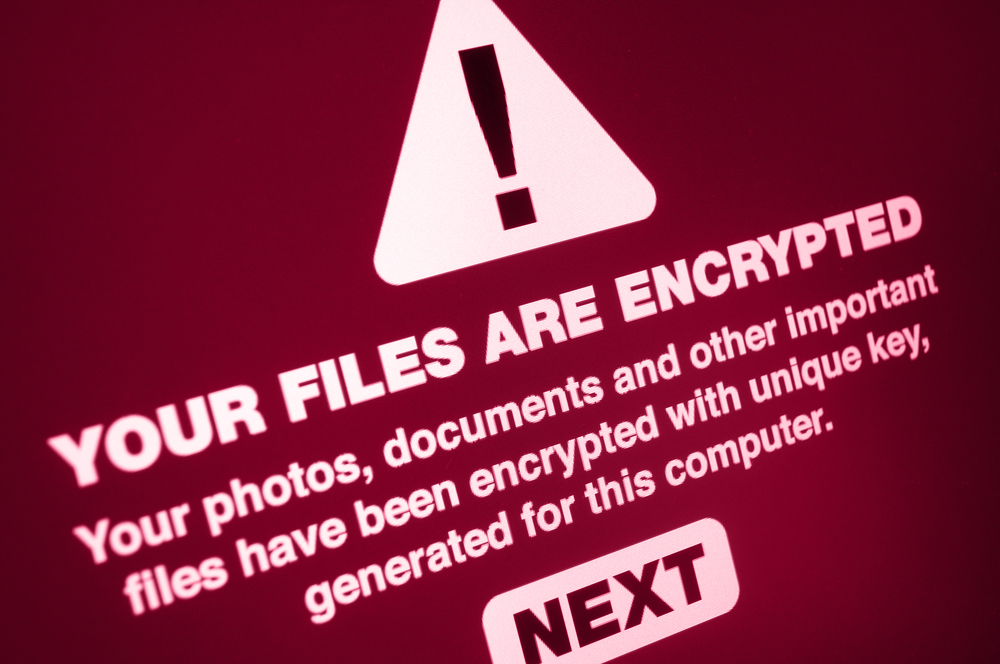
A security researcher named ‘SwitHak’ described that once the ransomware is executed, it targets DOC, DOT, WBK, DOCX, DOTX, DOCB, XLM, XLSX, XLTX, XLSB, XLW, PPT, POT, PPS, PPTX, POTX, PPSX, SLDX, and PDF files.
“If the ransomware is launched with the '-w' command line argument, though, it will target all file types. Other switches supported are '-k' and '-m' for base 64 encoding and for providing the emails addresses to show in the ransom note,” SwitHak explained, BleepingComputer reported.
BleepingComputer tested the ransomware sample and found that the code was very slow and made no effort to evade detection. Researchers noted that in the test, the sample launched itself with the -w argument and spawned a new process for each file it encrypted, which made the encryption process to be very slow.
Ransomware uses .locked extension for encrypted files
Researchers noted that while encrypting files, the ransomware appends the .locked extension to the encrypted file’s names. This indicates that the file named test.jpg would be renamed to test.jpg.locked once encrypted.
Once done with the encryption of the files on the system, the ransomware drops a ransom note named ‘README-NOW.txt’ on the desktop, which contains instructions to contact the CottleAkela@protonmail.com or QyavauZehyco1994@o2.pl email addresses for payment instructions.
LockerGoga signed with a valid certificate
A reverse engineer from McAfee detected that the ransomware strain is signed with a valid certificate. However, the signature is from MIKL limited and is for a host process for Windows services. Furthermore, the certificate issued by the Comodo Certificate Authority has been revoked.
“Known file samples for LockerGoga ransomware are ‘worker’ and ‘worker32’. The malware launches a process with a name similar to what Microsoft uses for its Windows Services, such as ‘svch0st’ or ‘svchub’,” researchers described.

Publisher








/https://cystory-images.s3.amazonaws.com/shutterstock_653153329.jpg)
/https://cystory-images.s3.amazonaws.com/iStock-605772798.jpg)
