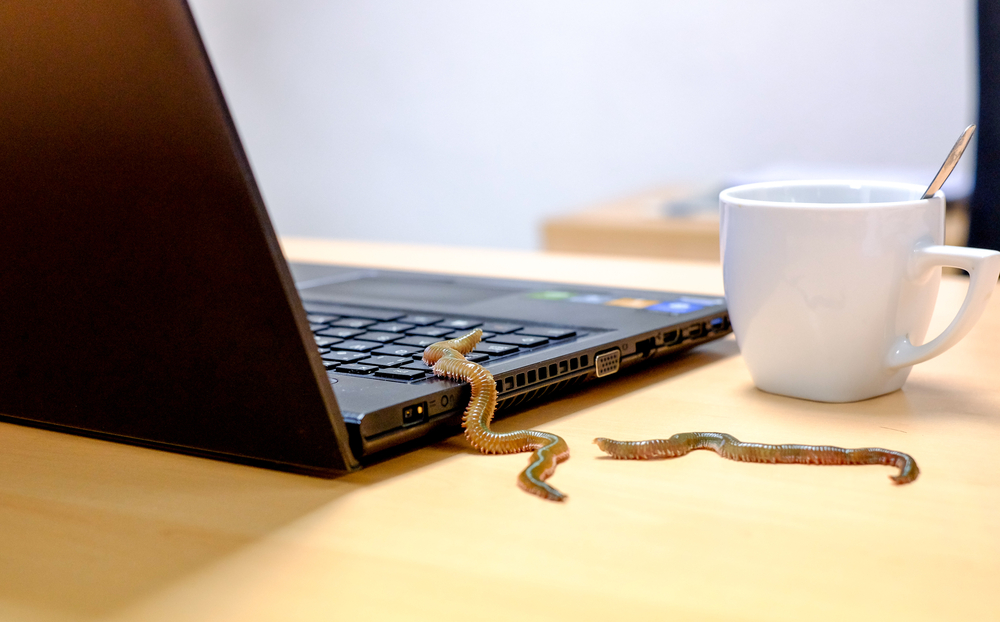
A new ransomware group, dubbed XingLocker, is actively using a customized MountLocker ransomware executable. This latest MountLocker operation uses Windows Active Directory APIs to propagate as a worm through networks. It has been active since July 2020.
What has happened?
Recently, the MalwareHunterTeam shared a sample of a new MountLocker executable. This new sample includes a worm feature that allows it to spread inside the network and encrypt to other devices.
- An attacker can enable the worm feature by executing the malware sample with the /NETWORK command-line argument. This feature requires a Windows domain to spread.
- Furthermore, the CEO of Advanced Intel discovered that MountLocker is now using the Windows Active Directory Service Interfaces API to work as a worm.
- Using this API, the ransomware can easily find all devices that are part of the infected Windows domain and then encrypt them with stolen domain credentials.
Recent MountLocker attacks
The ransomware has been active since earlier this year and has targeted several enterprise networks.
- Last month, the Astro Locker ransomware group started using a customized version of MountLocker. A connection was spotted between MountLocker and the Astro Locker team.
- In March, the MountLocker gang threatened to release stolen data from shipping firm ECU Worldwide. The gang had stolen 2TB of data belonging to the shipping firm.
Conclusion
MountLocker may be the first corporate ransomware using Active Directory-related APIs to perform reconnaissance and spread to other devices. Thus, organizations are recommended to stay vigilant and employ basic security measures, such as taking backup, regularly updating systems, and enabling 2FA.

Publisher








/https://cyware-ent.s3.amazonaws.com/image_bank/9f5a_shutterstock_1767348239.jpg)
/https://cyware-ent.s3.amazonaws.com/image_bank/c718_shutterstock_694458943.jpg)
